16. Setting up Social Authentication¶
Authentication methods help simplify logins for end users–offering single sign-ons using existing login information to sign into a third party website rather than creating a new login account specifically for that website.
Prior to Ansible Tower version 3.1, account authentication can only be configured in the /etc/tower/settings.py or the configuration files within /etc/tower/conf.d/. Starting with Ansible Tower version 3.1, instead of flat files, the configuration files are now saved to the Postgres database. Therefore, it is important that account authentication be configured in the Ansible Tower User Interface. For instructions, refer to the Tower Configuration section.
This section describes setting up authentication for the following systems:
Account authentication in Ansible Tower can be configured to centrally use OAuth2, while enterprise-level account authentication can be configured for SAML, RADIUS, or even LDAP as a source for authentication information.
For websites, such as Microsoft Azure, Google or GitHub, that provide account information, account information is often implemented using the OAuth standard. OAuth is a secure authorization protocol which is commonly used in conjunction with account authentication to grant 3rd party applications a “session token” allowing them to make API calls to providers on the user’s behalf.
SAML (Security Assertion Markup Language) is an XML-based, open-standard data format for exchanging account authentication and authorization data between an identity provider and a service provider.
The RADIUS distributed client/server system allows you to secure networks against unauthorized access and can be implemented in network environments requiring high levels of security while maintaining network access for remote users.
16.1. Basic Authentication Settings¶
To enable or disable HTTP basic authentication as used in the API browser, edit the sessions.py file, setting the following line as either True or False:
AUTH_BASIC_ENABLED = False
After saving your changes, run the ansible-tower-service restart command to ensure your changes take effect.
16.2. Google OAuth2 Settings¶
To set up social authentication for Google, you will need to obtain an OAuth2 key and secret for a web application. To do this, you must first create a project and set it up with Google. Refer to https://support.google.com/googleapi/answer/6158849 for instructions. If you already completed the setup process, you can access those credentials by going to the Credentials section of the Google API Manager Console. The OAuth2 key (Client ID) and secret (Client secret) will be used to supply the required fields in the Ansible Tower User Interface.
In the Ansible Tower User Interface, click Configure Tower from the Settings (
 ) Menu screen.
) Menu screen.
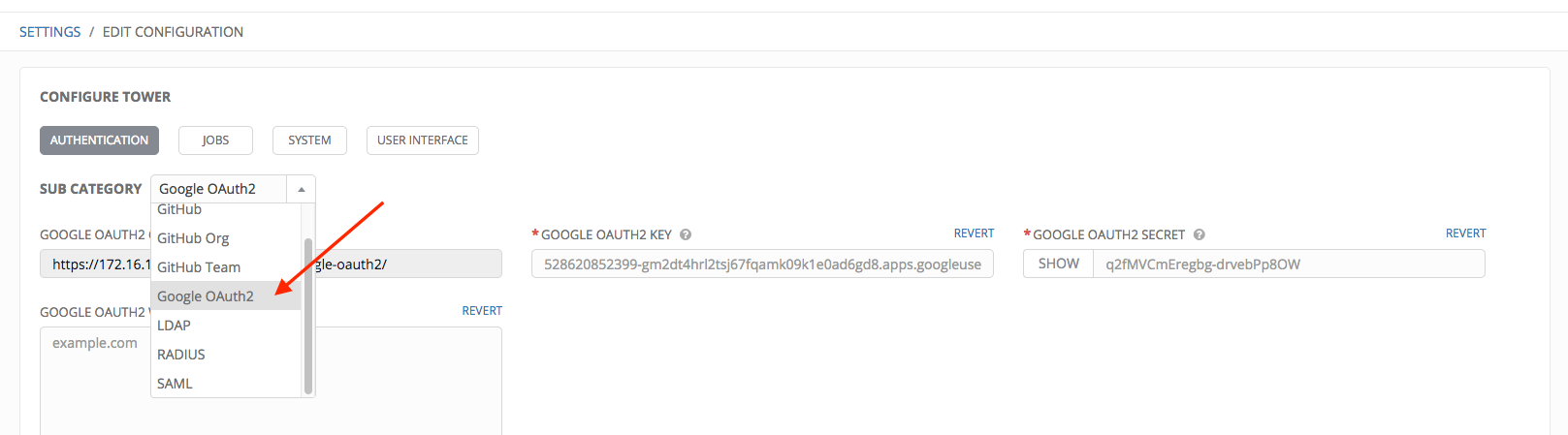
The Authentication tab displays initially by default.
In the Sub Category field, select Google OAuth2 from the drop-down list.
The Google OAuth2 Callback URL field is already pre-populated and non-editable.
Using the credentials Google supplied during the web application setup process:
Copy and paste Google’s Client ID into the Google OAuth2 Key field of the Configure Tower - Authentication screen. Look for the value with the same format as the one shown in the text field.
Copy and paste Google’s Client secret into the Google OAuth2 Secret field of the Configure Tower - Authentication screen. Look for the value with the same format as the one shown in the text field.
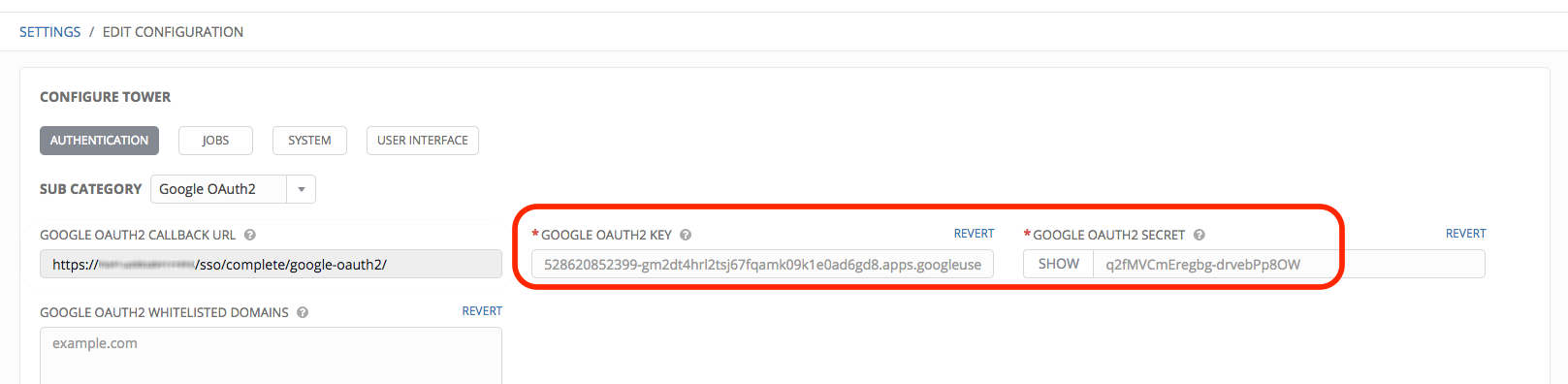
To complete the remaining optional fields, refer to the tooltips in each of the fields for instructions and required format.
For details on completing the mapping fields, see Organization and Team Mapping.
Click Save when done.
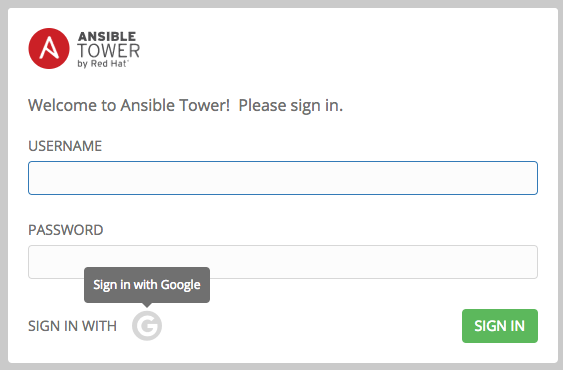
To verify that the authentication was configured correctly, logout of Ansible Tower and the login screen will now display the Google logo to indicate it as a alternate method of logging into Ansible Tower.
16.3. GitHub OAuth2 Settings¶
To set up social authentication for GitHub, you will need to obtain an OAuth2 key and secret for a web application. To do this, you must first register the new application with GitHub at https://github.com/settings/developers. In order to register the application, you must supply it with your homepage URL, which is the Callback URL shown in the Configure Tower user interface. The OAuth2 key (Client ID) and secret (Client Secret) will be used to supply the required fields in the Ansible Tower User Interface.
In the Ansible Tower User Interface, click Configure Tower from the Settings (
 ) Menu screen.
) Menu screen.
The Authentication tab displays initially by default.
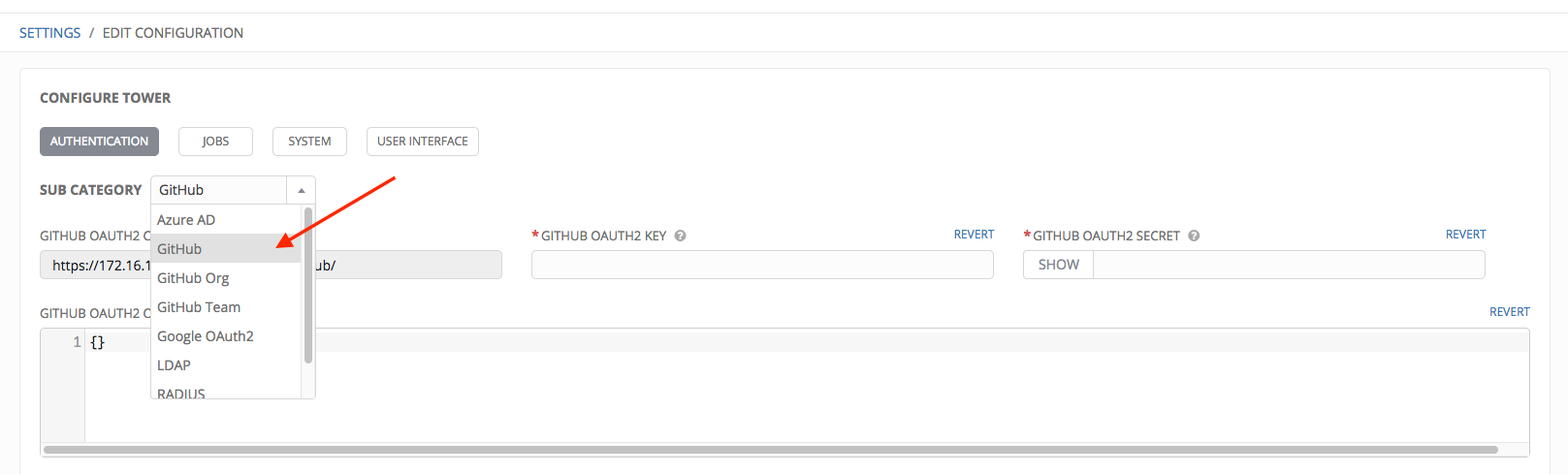
In the Sub Category field, select GitHub from the drop-down list.
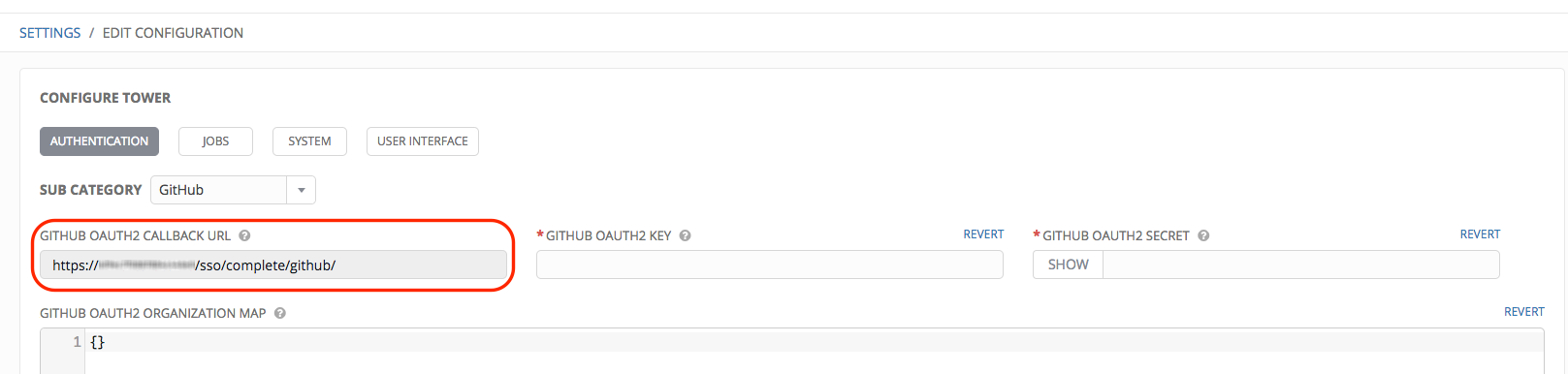
Use the GitHub OAuth2 Callback URL to supply GitHub when it prompts for your application’s Homepage URL.
Once the application is registered, GitHub displays the Client ID and Client Secret.
Copy and paste GitHub’s Client ID into the GitHub OAuth2 Key field of the Configure Tower - Authentication screen.
Copy and paste GitHub’s Client Secret into the GitHub OAuth2 Secret field of the Configure Tower - Authentication screen.
For details on completing the mapping fields, see Organization and Team Mapping.
Click Save when done.
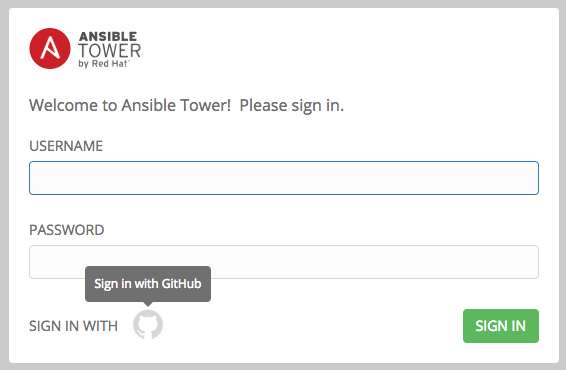
To verify that the authentication was configured correctly, logout of Ansible Tower and the login screen will now display the GitHub logo to allow logging in with those credentials.
16.3.1. Github Org Settings¶
When defining account authentication with either an organization or a team within an organization, you should use the specific organization and team settings. Account authentication can be limited by an organization as well as by a team within an organization.
You can also choose to allow all by specifying non-organization or non-team based settings (as shown above).
You can limit users who can login to Tower by limiting only those in an organization or on a team within an organization.
To set up social authentication for a GitHub Organization, you will need to obtain an OAuth2 key and secret for a web application. To do this, you must first register your organization-owned application at https://github.com/organizations/<yourorg>/settings/applications. In order to register the application, you must supply it with your Authorization callback URL, which is the Callback URL shown in the Configure Tower user interface. Each key and secret must belong to a unique application and cannot be shared or reused between different authentication backends. The OAuth2 key (Client ID) and secret (Client Secret) will be used to supply the required fields in the Ansible Tower User Interface.
In the Ansible Tower User Interface, click Configure Tower from the Settings (
 ) Menu screen.
) Menu screen.
The Authentication tab displays initially by default.
In the Sub Category field, select GitHub Org from the drop-down list.
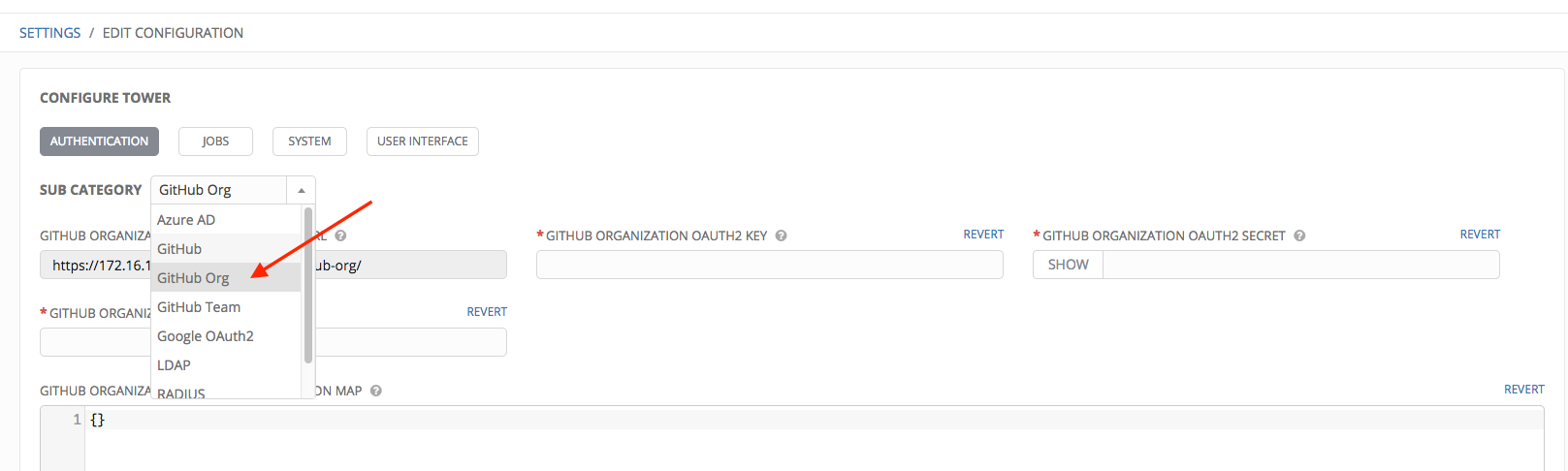
Use the GitHub Organization OAuth2 Callback URL to supply GitHUb when it prompts for the Authorization callback URL.
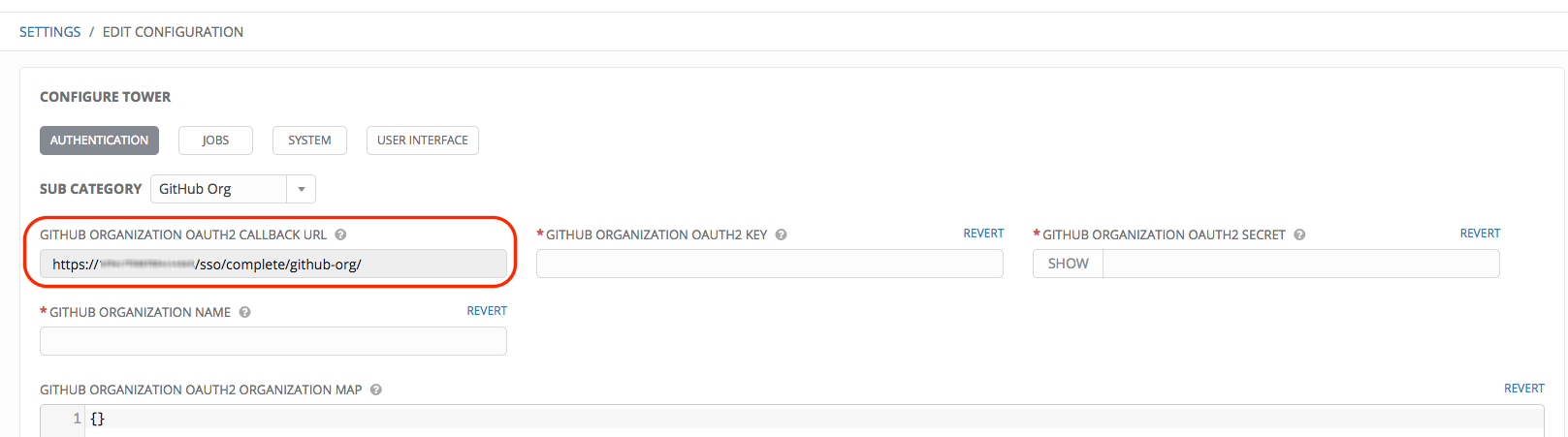
Once the application is registered, GitHub displays the Client ID and Client Secret.
Copy and paste GitHub’s Client ID into the GitHub Organization OAuth2 Key field of the Configure Tower - Authentication screen.
Copy and paste GitHub’s Client Secret into the GitHub Organization OAuth2 Secret field of the Configure Tower - Authentication screen.
For details on completing the mapping fields, see Organization and Team Mapping.
Click Save when done.
To verify that the authentication was configured correctly, logout of Ansible Tower and the login screen will now display the GitHub Organization logo to allow logging in with those credentials.

16.3.2. Github Team Settings¶
To set up social authentication for a GitHub Team, you will need to obtain an OAuth2 key and secret for a web application. To do this, you must first register your team-owned application at https://github.com/organizations/<yourorg>/settings/applications. In order to register the application, you must supply it with your Authorization callback URL, which is the Callback URL shown in the Configure Tower user interface. Each key and secret must belong to a unique application and cannot be shared or reused between different authentication backends. The OAuth2 key (Client ID) and secret (Client Secret) will be used to supply the required fields in the Ansible Tower User Interface.
Find the numeric team ID using the Github API: http://fabian-kostadinov.github.io/2015/01/16/how-to-find-a-github-team-id/. The Team ID will be used to supply a required field in the Ansible Tower User Interface.
In the Ansible Tower User Interface, click Configure Tower from the Settings (
 ) Menu screen.
) Menu screen.
The Authentication tab displays initially by default.
In the Sub Category field, select GitHub Team from the drop-down list.
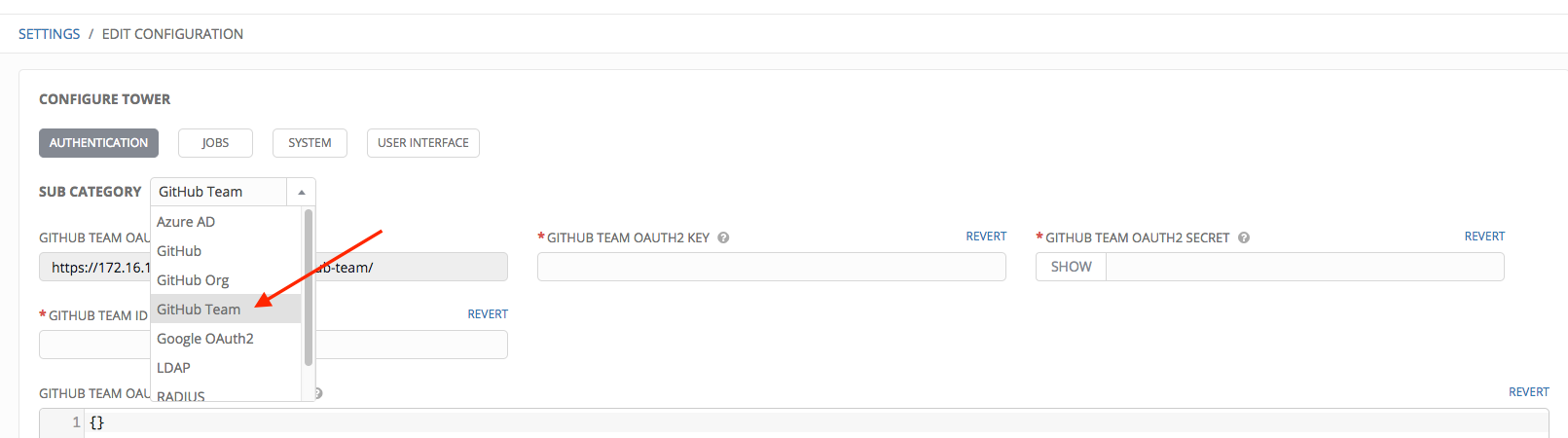
Use the GitHub Team OAuth2 Callback URL to supply GitHUb when it prompts for the Authorization callback URL.
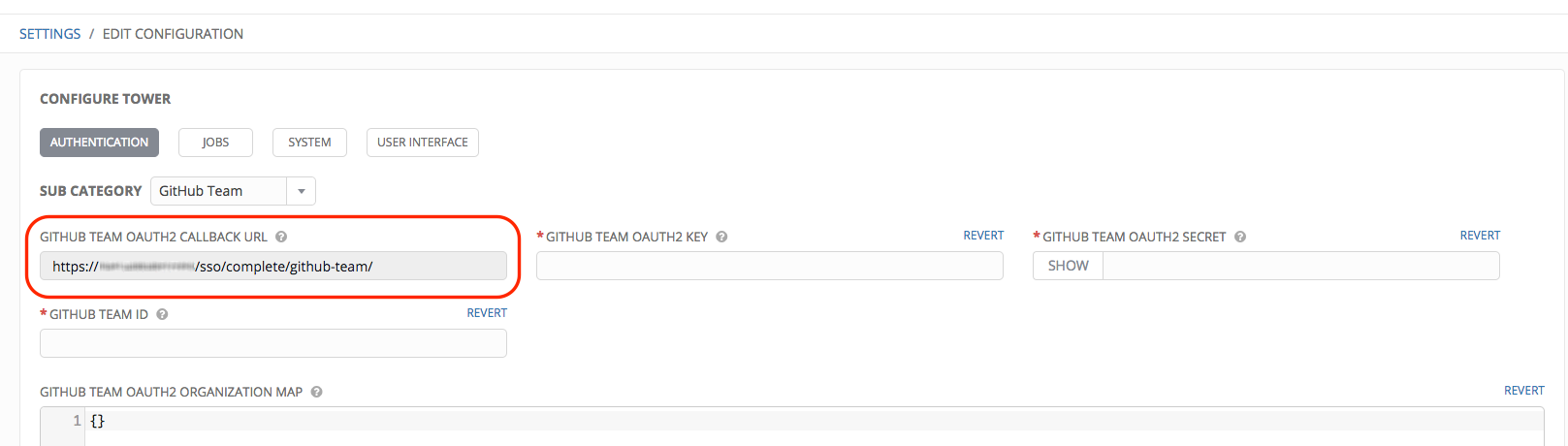
Once the application is registered, GitHub displays the Client ID and Client Secret.
Copy and paste GitHub’s Client ID into the GitHub Team OAuth2 Key field of the Configure Tower - Authentication screen.
Copy and paste GitHub’s Client Secret into the GitHub Team OAuth2 Secret field of the Configure Tower - Authentication screen.
For details on completing the mapping fields, see Organization and Team Mapping.
Click Save when done.
To verify that the authentication was configured correctly, logout of Ansible Tower and the login screen will now display the GitHub Team logo to allow logging in with those credentials.
16.4. Organization and Team Mapping¶
16.4.1. Organization mapping¶
You will need to control which users are placed into which Tower organizations based on their username and email address (mapping out your organization admins/users from social or enterprise-level authentication accounts).
Dictionary keys are organization names. Organizations will be created, if not already present and if the license allows for multiple organizations. Otherwise, the single default organization is used regardless of the key.
Values are dictionaries defining the options for each organization’s membership. For each organization, it is possible to specify which users are automatically users of the organization and also which users can administer the organization.
admins: None, True/False, string or list/tuple of strings.
If None, organization admins will not be updated.
If True, all users using account authentication will automatically be added as admins of the organization.
If False, no account authentication users will be automatically added as admins of the organization.
If a string or list of strings, specifies the usernames and emails for users who will be added to the organization. Strings beginning and ending with
/will be compiled into regular expressions; modifiersi(case-insensitive) andm(multi-line) may be specified after the ending/.
remove_admins: True/False. Defaults to True.
When True, a user who does not match is removed from the organization’s administrative list.
users: None, True/False, string or list/tuple of strings. Same rules apply as for admins.
remove_users: True/False. Defaults to True. Same rules apply as for remove_admins.
{
"Default": {
"users": true
},
"Test Org": {
"admins": ["[email protected]"],
"users": true
},
"Test Org 2": {
"admins": ["[email protected]", "/^tower-[^@]+?@.*$/i"],
"users": "/^[^@].*?@example\\.com$/"
}
}
Organization mappings may be specified separately for each account authentication backend. If defined, these configurations will take precedence over the global configuration above.
SOCIAL_AUTH_GOOGLE_OAUTH2_ORGANIZATION_MAP = {}
SOCIAL_AUTH_GITHUB_ORGANIZATION_MAP = {}
SOCIAL_AUTH_GITHUB_ORG_ORGANIZATION_MAP = {}
SOCIAL_AUTH_GITHUB_TEAM_ORGANIZATION_MAP = {}
SOCIAL_AUTH_SAML_ORGANIZATION_MAP = {}
16.4.2. Team mapping¶
Team mapping is the mapping of team members (users) from social auth accounts. Keys are team names (will be created if not present). Values are dictionaries of options for each team’s membership, where each can contain the following parameters:
organization: string. The name of the organization to which the team belongs. The team will be created if the combination of organization and team name does not exist. The organization will first be created if it does not exist. If the license does not allow for multiple organizations, the team will always be assigned to the single default organization.
users: None, True/False, string or list/tuple of strings.
If None, team members will not be updated.
If True/False, all social auth users will be added/removed as team members.
If a string or list of strings, specifies expressions used to match users. User will be added as a team member if the username or email matches. Strings beginning and ending with
/will be compiled into regular expressions; modifiersi(case-insensitive) andm(multi-line) may be specified after the ending/.
remove: True/False. Defaults to True. When True, a user who does not match the rules above is removed from the team.
{
"My Team": {
"organization": "Test Org",
"users": ["/^[^@]+?@test\\.example\\.com$/"],
"remove": true
},
"Other Team": {
"organization": "Test Org 2",
"users": ["/^[^@]+?@test\\.example\\.com$/"],
"remove": false
}
}
Team mappings may be specified separately for each account authentication backend, based on which of these you setup. When defined, these configurations take precedence over the the global configuration above.
SOCIAL_AUTH_GOOGLE_OAUTH2_TEAM_MAP = {}
SOCIAL_AUTH_GITHUB_TEAM_MAP = {}
SOCIAL_AUTH_GITHUB_ORG_TEAM_MAP = {}
SOCIAL_AUTH_GITHUB_TEAM_TEAM_MAP = {}
SOCIAL_AUTH_SAML_TEAM_MAP = {}
Uncomment the line below (i.e. set SOCIAL_AUTH_USER_FIELDS to an empty list) to prevent new user accounts from being created. Only users who have previously logged in to Tower using social or enterprise-level authentication or have a user account with a matching email address will be able to login.
SOCIAL_AUTH_USER_FIELDS = []